Azure Security Best Practice Guide
This Azure security best practice guide will help you improve, scale, and centralize your cloud security. We have compiled these best practices based on our experience, including:
- Limiting Access to Sensitive Data
- Implementing Threat Protection and Safeguards
- Centralizing and Managing Security
Limiting Access to Sensitive Data
- Implement a Zero Trust security model
- Verify explicitly: Authenticate and authorize using all available data points, including user identity, location, device health, service, data classification, and anomalies.
- Use least-privileged access: Limit user access to data using risk-based adaptive policies and Just-in-Time and Just-Enough Access (JIT/JEA)
- Assume breach: Segment access by networks, user, devices, and application awareness. Encrypt all sessions end to end and use analytics to analyze and improve your existing defenses.
- Restrict access to management ports
- Use IP whitelisting (when applicable)
- Use Azure Disk Encryption to encrypt Azure VMs
- Secure your Azure Active Directory (AD) app registrations
- Use least privileged access. Grant only the minimum set of permissions required for end users to perform the required tasks in an application, service, or system.
- Clearly define app registration credentials. Credentials are key when using app registrations as a confidential client. If your app registration is used only as a Public Client App (allows users to sign in using a public endpoint), ensure that you don't have any credentials on your application object.
- Minimize app ownership. Once a quarter, run through the app owners list to ensure owners are still part of the organization.
- Use Privileged Identity Management (PIM)
The Zero Trust model is a security model that constantly checks whether users within the system should have access to certain files and systems. With hybrid work on the rise, cyberattacks jumped 238%. From a security standpoint, it’s more important now than ever to plan for the worst-case scenario. The Zero Trust model operates on the principle of “never trust, always verify.” It assumes the corporate firewall has already been breached and verifies each request that comes through as if it was coming from an uncontrolled network.
The Zero Trust model’s guiding principles are:
Management ports are the ports you use to connect to your Azure virtual machines (VMs). Remote Desktop Protocol (RDP - 3389) and the Secure Shell (SSH - 22) protocol are commonly used management ports that enable admins to manage VMs from remote locations. However, using these protocols over the internet enables attackers to use brute force techniques to gain access to VMs. For example, attackers have been known to scan public cloud IP ranges for known vulnerabilities and common passwords.
Mitigate the risk by restricting access to management ports with techniques like just-in-time (JIT) VM access to lock down inbound traffic to your Azure VMs.
IP restrictions enable you to define which IP addresses can access your service. Whitelisting IP addresses prevents unwanted or unauthorized machines from accessing the service. The “allow” list can include individual IP addresses or a range of IP addresses defined by a subnet mask. This gives you close control over who can access your cloud data. Don’t assign allow rules with broad ranges (for example, “allow 0.0.0.0 through 255.255.255.255”).
Even when whitelisting IP address, protect your virtual network using Azure Firewall. On top of limiting access to IP ranges, restrict access to limited ports.
Most Azure managed disks are automatically encrypted via server-side encryption (SSE) with a platform-managed key (PMK). For OS and data disks, you should also enable Azure Disk Encryption (ADE). This way, your data has two levels of protection. ADE helps protect and safeguard your data by using Azure Key Vault to control and manage encryption keys and secrets. With only SSE enabled, downloaded VHD files will be decrypted and can be used to create a new VM. With both SSE and ADE enabled, users cannot use downloaded VHD files to create a new VM unless provided the decryption key.
Similarly, always enable Transparent Data Encryption (TDE) on SQL databases to secure data at rest
Azure AD app registrations are a critical part of your business and security operations. Any misconfiguration or lapse in app hygiene not only increases downtime for end users, but actually compromises the entire system. To ensure your Azure AD app registrations are secure, implement the following practices:
PIM is an Azure AD service that enables you to manage, control, and monitor access to key resources in your organization. With PIM, you can provide as-needed and just-in-time (JIT) access to Azure resources and other online Microsoft services such as Microsoft 365 and Microsoft Intune. PIM provides time-based and approval-based role activation. This reduces the chance of a malicious attacker gaining access to your system. It also limits authorized users inadvertently impacting sensitive resources.
Implementing Threat Protection and Safeguards
- Enable Azure Defender
- Enable Multi-factor Authentication (MFA)
- Maintain platform hygiene
- Turn off Azure services and servers when not in use and remove inactive resources
- Set up locks on your resource groups
Formerly known as Azure Advanced Threat Protection (ATP), Azure Defender protects enterprise environments from targeted cyber-attacks and insider threats. Azure Defender is a part of the Azure Security Center. It detects threats throughout the phases of an advanced attack, including reconnaissance, credential compromise, lateral movement, privilege escalation, and domain dominance. Azure Defender is ideal for both cloud-native and hybrid workload protection. Early threat detection is the key to halting attacks before they impact your business.
Multi-factor authentication, also known as two-factor authentication, adds a secondary layer of security to your systems. Azure AD MFA verifies user identities via phone call, text message, or mobile app notification. Azure AD MFA replaces outdated username and password authentication, restricting unauthorized access. Because Azure AD MFA requires access to a user’s phone, the user’s data and applications are protected even if the user’s password is compromised. Organizations that do not add this extra layer of identity protection are more susceptible to credential theft.
A clean platform is a secure platform. Clean up your Azure subscription by removing deprecated identities, users, and resources. Periodically review access for existing users in your subscription. Follow Azure Security Center guidelines by ensuring no more than three individuals are identified as subscription owners.
Only turn on the services you are actively using. This will not only reduce the surface area of security threats, it will also reduce the cost of Azure services. You shouldn’t be paying for a service you aren’t using. To manage resources, create runbooks that automatically turn resources on/off at scheduled times.
Locks safeguard the development teams from accidentally deleting resources.
Centralizing and Managing Security
- Use the Azure Security Center
- Instantly implement Azure-native security solutions
- Manage security policy and compliance
- Continuously assess security status with real-time monitoring
- Access a network map
- Improve security by following recommended controls for each Azure service
- Protect against threats on both infrastructure as a service (IaaS) and platform as a service (PaaS) environments
- Azure Secure Score, which measures the security status of your subscriptions (a higher score means lower risk level)
- Azure Defender Status (for all enabled resource types)
- Inventory of resource health state
- Regulatory compliance such as SOC TSP, ISO 27001, PCO DSS 3.2.1 (you can enable the platform’s out-of-the-box compliance controls or input custom controls)
- High-impact security recommendations and the potential percentage increase in Azure Secure Score if implemented
- Use Azure Web Application Firewall (WAF) on Azure Application Gateway
- Use Azure Active Directory (AD) to manage identities and access to cloud applications
- Assign resource access to Active Directory groups, not individuals
- Use Azure Key Vault
- Limit user and identity access to certificates, secrets, and keys
- Enable soft delete to retrieve objects that have been accidentally deleted from the key vault
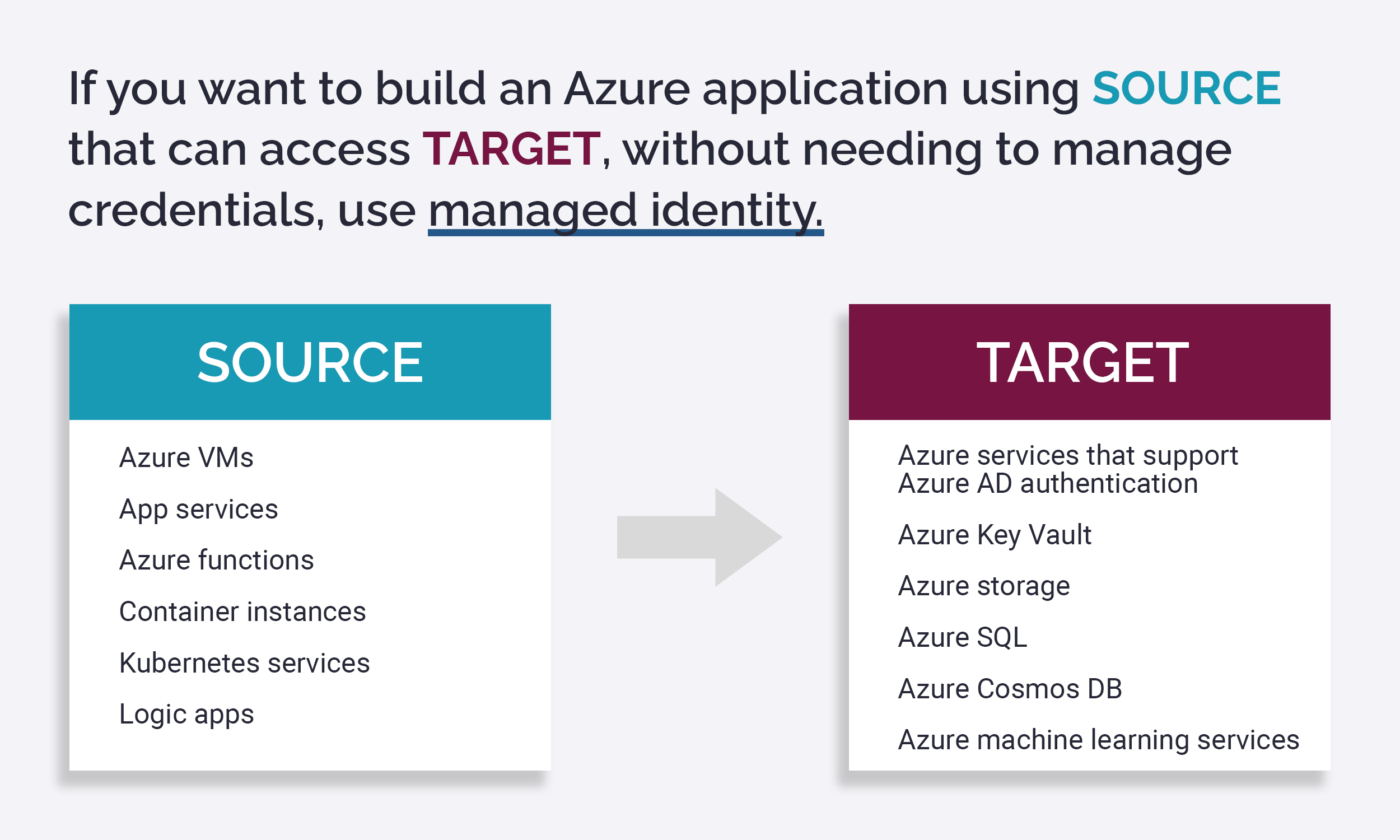
- Use managed identity wherever possible
- Remove in-development copies of databases
- Update your system as often as possible
Azure Security Center is a worthwhile investment to secure your cloud assets and view your security status. Azure Security Center uses machine learning and advanced analytics to detect existing and potential threats, and suggest preventative actions. With Azure Security Center, you can:
How to use Azure Security Center:
Define your security admins. The security admin role handles alerts, Azure Defender, security policy, and the auto provisioning of log analytics and extensions. As a rule of thumb, developers should be classified using the Security Reader role.
To review your security status using Azure Security Center, go to the Azure menu and select Security Center>Overview. You will see:
WAF centralizes your web app protection to enable easy monitoring and customization. WAF protects your web apps from vulnerabilities, common exploits, and malicious attacks. WAF protects against cross-scripting and SQL injection attacks, some of the most common web attacks in the last few years.
WAF also automatically updates to include protections against new vulnerabilities, without the need to add additional configurations.
Azure AD is a multi-tenant cloud directory and identity management service. Azure AD secures and simplifies user access to cloud applications with single sign-on. According to Microsoft, Azure AD protects users from 99.9% of cybersecurity attacks. Azure AD also protects sensitive data and applications with multi-factor authentication and machine learning-based reports, which identify inconsistent access patterns.
Many organizations give individual developers access to resources such as Azure VMs or SQL Servers when they begin work on a project. When those developers move to a different project, it becomes difficult to keep track of access privileges that are no longer required. Individual permissions often remain active even when the individual is no longer assigned to the project. By assigning access to Azure AD groups instead of individuals, you simplify access management and ensure that developers only have access to resources for their projects. The group owner is empowered to ensure that only those who are currently assigned to the project have access to its data.
Periodically review your Azure AD groups. Assign roles based on least privileged access policies, with subscription always restricted to a reader role.
Azure Key Vault safeguards cryptographic keys and secrets used by cloud applications and services. With this feature, you can ensure applications never have direct access to keys. Developers manage keys used for Dev/Test and can seamlessly migrate keys managed by security operations to production.
When using Azure keys, ensure you:
A managed identity in Azure Active Directory (AAD) enables applications to easily access other AAD-protected resources such as Azure Key Vault. The Azure platform manages identities, eliminating the need to provision or rotate secrets.
Managed identity also automatically renews service principals, which should always be enabled. Service principals are AAD application resources that perform unattended resource and service-level operations.
During the software development process, programmers create copies of existing databases to test their code. Additional backups are created during system software upgrades when installing new versions of applications. Over time, developers move on to new projects. Often, after moving to a new project, developers do not remove unused copies and files from previous systems. Leaving clutter on the server and file store is like leaving tools on the floor of a factory. Someone is bound to trip and get hurt.
Security starts and ends with discipline. To keep track of your resources, create an automated runbook that informs admins of historical databases. Remove any resource you aren’t using. This will ensure your workspace is clean and organized.
Today’s internet landscape features evolving security threats. To outpace cybersecurity attackers, Microsoft continually updates its products and services. Update your own resources when the newest patches release to ensure your security system is up to date and secure.
References
- Azure security best practices and patterns – Microsoft Corporation, published March 22, 2023
- Azure network security best practices – Microsoft Corporation, published March 16, 2023
- Azure Identity Management and access control security best practices – Microsoft Corporation, published December 19, 2022
- Embrace proactive security with Zero Trust – Microsoft Corporation
